Moussaoui Evades Death, Receives Life in Prison - 3/5/06

4Law 3/5/06
Jurors Reject Death Penalty For Moussaoui
Al-Qaeda conspirator Zacarias Moussaoui will spend the rest of his life in a maximum security prison for his role in the Sept. 11 attacks after a federal jury rejected the government's four-year quest to secure his execution for the deadliest terrorist strike on U.S. soil.After weeks of listening to harrowing testimony from 9/11 family members, hearing heartbreaking emergency calls and watching painful footage of victims jumping to their deaths, the anonymous jury of nine men and three women methodically deliberated for 41 hours over seven days before reaching its verdict today.Jurors carefully went over each question on a 42-page verdict form that gave only a few clues to their thoughts and reasoning. In the end, though, the form indicated that prosecutors could not surmount the main obstacle hanging over their case from the start: Moussaoui did not hijack anything Sept. 11, 2001, because he was sitting in jail.The panel could not decide unanimously that Moussaoui caused the nearly 3,000 deaths, nor could it agree that he committed his crimes "in an especially heinous, cruel or depraved manner." Three jurors took it upon themselves to write that Moussaoui had "limited knowledge of the 9/11 attack plans."Moussaoui, 37, is the only person charged in a U.S. courtroom in connection with the attacks, in which planes were crashed into the World Trade Center, the Pentagon and a Pennsylvania field. After four years of delays, twists and turns in his criminal case, he pleaded guilty last year to conspiracy.He will live out his days in the nation's super-maximum security prison in Florence, Colo. Prosecutors cannot appeal the jury's decision, which is technically a recommendation but which U.S. District Judge Leonie M. Brinkema is legally bound to uphold. She is scheduled to formally sentence Moussaoui tomorrow morning.The verdict was a resounding victory for Moussaoui's defense team, which battled through the higher and lower courts for a client who admitted allegiance to Osama bin Laden, vowed to kill Americans, pleaded guilty against lawyers' advice to the country's worst crime, fought them at every turn and visibly despised them.
Moussaoui Evades Death, Receives Life in Prison - 3/5/06
FOX TV 3/5/06 Save as or Open...
Moussaoui Gets Life - Moussaoui Reaction
Lawyer Reaction - Prosecutor Reaction
Moussaoui Eligible for Death Penalty - 3/4/06
FindLaw :Special Verdict Form approved by the court for the jury to use in deciding whether or not to sentence Moussaoui to death. [HTML] (March 24, 2006)
FOX TV 3/4/06
Sept. 11 Kin Closer to Closure? - Moussaoui Eligible for Death
Pentagon
Attack1 - Pentagon
Attack2 - Bush
talks on the Attack
| Moussaoui E - Mail & The E - Mail in the Indictment |
|
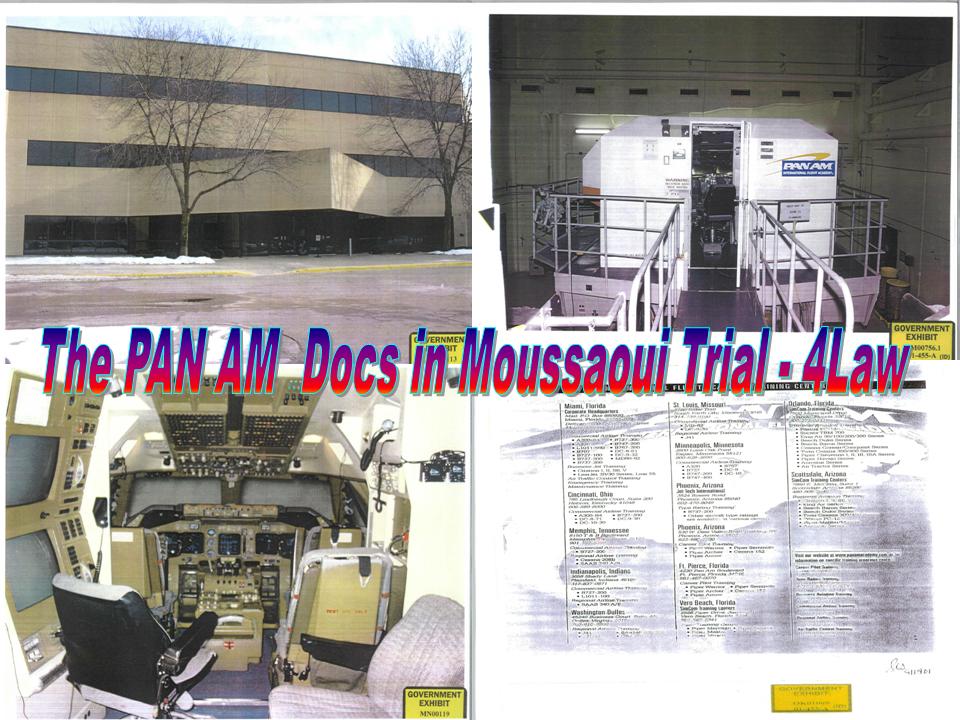
51. On or about May 23, 2001, ZACARIAS MOUSSAOUI contacted an office of the Pan Am International Flight Academy in Miami, Florida via e-mail. MOUSSAOUI Purchases Flight Training Equipment 56. On or about June 20, 2001, ZACARIAS MOUSSAOUI purchased flight deck videos for the Boeing 747 Model 400 and the Boeing 747 Model 200 from the Ohio Pilot Store. MOUSSAOUI Pays for Flight Lessons 60. On or about July 10 and July 11, 2001, ZACARIAS MOUSSAOUI made credit card payments to the Pan Am International Flight Academy for a simulator course in commercial flight training. MOUSSAOUI Takes Commercial Flying Lessons in Minnesota 71. On or about August 10, 2001, in Minneapolis, Minnesota, ZACARIAS MOUSSAOUI paid approximately $6,300 in cash to the Pan Am International Flight Academy. 72. Between August 13 and August 15, 2001, ZACARIAS MOUSSAOUI attended the Pan Am International Flight Academy in Minneapolis, Minnesota, for simulator training on the Boeing 747 Model 400. |
 |
 |
|
FOR THE EASTERN DISTRICT OF VIRGINIA Alexandria Division |
||
UNITED STATES OF AMERICA
v.ZACARIAS MOUSSAOUI, Defendant |
)
) ) ) ) ) ) |
Criminal No. 01-455-A |
GOVERNMENTS OPPOSITION TO
STANDBY COUNSELS REPLY TO THE GOVERNMENTS
RESPONSE TO COURTS ORDER ON COMPUTER AND E-MAIL EVIDENCE
The United States respectfully responds to Standby Counsels Reply to the Governments Response to the Courts Order on Computer and E-Mail Evidence (hereafter Reply) as follows:
Authentication
The foundation of standby counsels discovery requests regarding the computer and e-mail evidence rests upon their complaints regarding the authentication of the hard drives provided in discovery. Authentication in this context means the process of ensuring that the duplicate of the hard drive provided in discovery is an exact copy of what the FBI originally acquired. As FBI Supervisory Special Agent Dara Sewell explains in her attached affidavit, the FBI uses three different methods to duplicate or image a hard drive:1
(1) GNU/Linux routine dd command via Red Hat Linux 7.1 (hereafter Linux dd);Sewell Affidavit at 2. Standby counsel seek the complete authentication information for all of the hard drives produced in discovery, particularly the information for Mr. Moussaouis laptop, the University of Oklahoma system, and Mukkarum Alis laptop. Reply at 8.(2) Safeback version 2.18 imaging software by New Technologies (hereafter Safeback);
(3) Solitaire Forensics Kit, SFK-000A hand-held disk duplicator by Logicube, Inc. (hereafter Logicube).
____________________
1 In very simple terms, an image of a restored hard drive is to that restored hard drive what a negative is to a photograph.Before addressing the authentication for the four specific computers, an error in Mr. Allisons affidavit must be corrected. In his affidavit, Mr. Allison writes: Many methods are available to create an exact duplicate; however, only one method the GNU/Linux routine dd has been approved by the National Institute of Standards and Technologies. Allison Affidavit at 3. This statement is simply wrong. The National Institute of Standards and Technologies (NIST) does not approve software, it merely tests it and then publishes the results of its tests. NIST did, indeed, test Linux dd and publish the results, which included some criticism. Sewell Affidavit at 3. Like Linux dd, Safeback has also been submitted to NIST for review and its final report was published on December 13, 2002. Sewell Affidavit at 3. NIST reported criticisms of Safeback comparable to those cited for GNU/Linux routine dd. Sewell Affidavit at 3-4.2 Thus, for purposes of NIST, both Linux dd and Safeback are accurate imaging tools. With this in mind, the authentication of the four computers at issue follows.3
____________________
2 None of the criticisms of Safeback or Linux dd have any apparent bearing on the issues in this case. Sewell Affidavit at 3-4.More important, the manufacturers of both Safeback and Logicube engaged in extensive self-testing of their programs before marketing them. Further, both contain verification programs\functions that ensure that the image\duplicate accurately reflects the data contained on the original. Sewell Affidavit at 4-5. Finally, FBI CART has validated the use of both Safeback and Logicube during their own use of the methods on hundreds of computers. Sewell affidavit at 4-5. Both Safeback and Logicube, like Linux dd, are methods that are accepted within the forensic computer community. Sewell Affidavit at 4-5.3 A detailed discussion for all 140 hard drives provided in discovery is not set forth because, to do so, would take extensive (and unnecessary) manpower. As stated below, the Government has provided the defense with a list of all hard drives and their source. All hard drives in this case were imaged by one of the three programs used by the FBI, all of which are recognized by the scientific community as reliable imaging programs. Thus, there should be no question about the authenticity of any of the hard drives. However, if the defense has additional questions about a specific hard drive other than the four at issue, the Government will answer those questions to the best of its ability.
Additionally, Mr. Allison writes: Further, once the duplicate has been created, a product such as the Message Digest version 5 (MD5) or the Secure Hash Algorithm version 1 (SHA-1) should be used to confirm that the duplication process has been done properly. Allison Affidavit at 3. Mr. Allison refers to programs that generate a unique value for both the data on the original hard drive and the data on a purported duplicate of that hard drive in order to further verify the results of the duplication process. However, as set forth in detail in SSA Sewells affidavit, both Safeback and Logicube contain self-validating programs that ensure the image or copy process generates an exact duplicate of the original. Sewell Affidavit at 4-6. Therefore, the MD5 or SHA-1 programs only provide an additional layer of verification beyond the already proven reliability of the tool itself. Sewell Affidavit at 6.
Both defendants and Mukkarum Alis laptops were duplicated using the Safeback software. To eliminate any questions about authentication, the FBI employed the MD5 program suggested by Mr. Allison on both laptops. The program demonstrated that the images of both laptops provided to the defense in discovery were accurate reproductions of the originals. Sewell Affidavit at 7-10. The significance of this point is two-fold. First, there can be no question that the defense has the exact same copy of the original that the Government has, so they can conduct any further investigation on their copy that they wish. Second, the results of the MD5 program as to these two laptops further demonstrate the reliability of the Safeback program.
Finally, standby counsel seek the BIOS (Basic Input/Output System) settings for defendants laptop based upon the following assertion by Mr. Allison in his affidavit:
The complete authentication information for Mr. Moussaouis laptop is even more critical given the indication in the above documents, particularly Bates no. M-LBR-0002265, that the laptop had lost all power by the time of the governments CART examination on August 6, 2002. [Footnote omitted]. The loss of all power means that the original date and time settings cannot be retrieved, and that other settings, such as how the computer performed its boot sequence, the types of ports and peripherals enabled, and the settings regarding the hard disk and the controller, are all lost as well. All of this is essential information on how the laptop was set up.Allison Declaration at 3-4. As SSA Sewell makes clear in her affidavit, however, the BIOS settings for defendants laptop were recorded at the time that it was imaged, September 11, 2001, before any loss of power. The BIOS settings are set forth in SSA Sewells affidavit. Sewell Affidavit at 11. Therefore, no authentication issues exist as to defendants or Mukkarum Alis laptops.4
____________________
4 In his Declaration, Mr. Allison requests the BIOS settings only for defendants laptop because of the loss of power for this computer. Allison Declaration at 4. Standby counsel go much farther in their motion by requesting the BIOS settings for all four hard drives at issue. Reply at 8-9. Since the Government has demonstrated the authentication of all of the hard drives and only defendants laptop lost power, there is no need for the BIOS settings for the other three hard drives.Unlike the laptops, the two hard drives at the University of Oklahoma (known as PC 11" and PC 14") were never removed from the university and are not currently in the Governments possession. Due to the nature of the hard drives, the FBI used the Logicube hand-held disk duplicator to copy the drives and then imaged the duplicates with the Safeback program. Logicube was selected to duplicate the University of Oklahoma hard drives because of its portability. Sewell Affidavit at 3-5, 18. Like Safeback, Logicube has been verified by both its manufacturer and the FBI. Moreover, Logicube performs self-checking functions to ensure that the duplicate drive accurately reflects the contents of the original drive. Finally, although Logicube has not yet been reviewed by the NIST, hand-held disk-duplicators such as Logicube are widely accepted in the information and forensic communities. Sewell Affidavit at 5. Consequently, there can be no challenge to the authenticity of the duplicates of the University of Oklahoma hard drives.
The Request for a Chart for the Remaining Hard Drives
Standby counsel next seek a chart for the approximately 140 remaining hard drives. At a minimum, the chart should include the origin/source for each drive and the significance of the drive to the case. Reply at 9.5 On November 22, 2002, the Government supplied the defense with a chart listing each hard drive produced in discovery, when it was produced, and a detailed description of its source from which the defense can assess its significance. Further, in a letter dated December 18, 2002, the Government identified the computer evidence that it believes to be relevant for this prosecution. Of course, the burden rests with the defense to determine the significance of a piece of evidence to their defense. Cf. United States v. Comosona, 848 F.2d 1110, 1115 (10 th Cir. 1988) (The Government has no obligation to disclose possible theories of the defense to a defendant. If a statement does not contain any expressly exculpatory material, the Government need not produce that statement to the defense. To hold otherwise would impose an insuperable burden on the Government to determine what facially non-exculpatory evidence might possibly be favorable to the accused by inferential reasoning.); United States v. Nachamie, 91 F. Supp. 2d 565, 569 (S.D.N.Y. 2000) (The clear language of Rule 16(a)(1), however, does not require the Government to identify which documents fall in each category it only requires the production of documents responsive to any category.); United States v. Greyling, 2002 WL 424655 at *3 (S.D.N.Y. 2002) (Fed. R. Cr. P. 16(a)(1)(C) only requires that the Government afford defendants an opportunity to inspect the documents it intends to introduce at trial. It does not require the Government to identify which documents it intends to introduce.) (emphasis in original). Therefore, this request is now moot.
____________________
5 Paradoxically, in making this request, standby counsel concede that the Government has far exceeded its discovery responsibilities regarding the computer evidence, which this request only expands; yet, the defense has failed to provide the Government with the first piece of discovery. See Reply at 4 (While we recognize that the Government may already have gone further with discovery in this area than would ordinarily be required . . . .).
Standby counsel next request the Court to [o]rder the Government to confirm that the UO hard drive produced in discovery has not been contaminated and explain why the 70 GB of unused storage space on that hard drive contains material that should not be there. Reply at 9. As the affidavit of SSA Sewell makes clear, the following answers Mr. Allisons concerns about University of Oklahoma PC 11. Approximately 9.537 gigabytes of information were duplicated from PC 11's hard drive by the Logicube program onto a 40 gigabyte drive. Thereafter, all data on the Logicube 40 gigabyte drive was imaged and later restored using the Safeback program onto a 80 gigabyte hard drive, which was then turned over to the defense. The primary partition which exists on the defense 80 gigabyte duplicate hard drive accurately represents the approximately 9.529 gigabytes captured from the primary partition of PC 11 without contamination. The balance of the space on the 80 gigabyte hard drive provided to the defense contains the following:
(1) Approximately 7.26 megabytes of data of the 9.537 gigabytes of data captured from PC 11. This information actually appeared on PC 11 outside of the primary partition and was duplicated by Logicube. Therefore, this data previously existed on the PC 11 and did not result from the imaging/duplication process;Sewell Affidavit at 19-20. All of this simply means that the first 9.537 gigabytes of the 80 gigabyte hard drive provided to the defense accurately contains all of the data that existed on PC 11 at the time of duplication and was not contaminated by any outside data.(2) Unused space which consists of a series of zeroes; and,
(3) Approximately 4 megabytes of repetition of the 9.537 gigabytes of information captured from PC 11, which was created by the Logicube tool when it first began to duplicate the material contained on PC 11.6
____________________
6 In very simple terms, the Logicube tool essentially made sure it could duplicate the information contained on PC 11 before it began copying it. This test information appeared in the defense duplicate because the hard drive was much larger than the 9.5 gigabytes of information duplicated from the PC 11 by the Logicube program. Sewell Affidavit at 20 n. 3.
Standby counsels fourth request questions whether the defendants laptop was imaged before it lost power. The defendants laptop was imaged on September 11, 2001, before the laptop lost power. Sewell Affidavit at 11. The BIOS settings for the laptop requested by standby counsel are set forth in SSA Sewells affidavit. Sewell Affidavit at 11. Therefore, this request is now moot.
The xdesertman@hotmail Account and Other E-Mail Accounts
In their fifth request, standby counsel ask the Court to [o]rder the Government to examine all of the temporary files of the computers Mr. Moussaoui used (those at UO, his laptop, and Mukkarum Alis laptop) and determine whether information can be obtained from them concerning the xdesertman@hotmail.com account and the other email accounts listed in paragraph 33 of the Lawler Affidavit. Reply at 10. SSA Sewells affidavit describes the unsuccessful searches of each hard drive conducted by FBI CART Field Examiner Thomas Lawler for the xdesertman@hotmail.com e-mail account as well as at least 27 variations of this account and other e-mail accounts associated with the investigation of this case. Sewell Affidavit at 15. Moreover, as previously demonstrated in the first section of this pleading addressing the authentication issues, the defense now has an exact copy of what the Government has. Therefore, there is no reason that the defense, including their computer expert, cannot conduct the same examinations of the four hard drives at issue as the Government. Consequently, this request should be denied.
Similarly, in their sixth request, standby counsel ask the Court to order the Government to conduct an investigation at their behest when they have the same ability to conduct the investigation. The defense possesses the same subpoena power as the Government and, if they wish to serve a subpoena on Hotmail, Microsoft, or any other company, they should do so. See Fed. R. Crim. P. 17(c); 18 U.S.C. § 3005. Moreover, the Group Manager for Policy Enforcement for MSN Hotmail reports that a search as suggested by Mr. Allison in his Declaration (see Allison Declaration at 6) would have no success. Sewell Affidavit at 21-22. Therefore, this request should fail.
The Internet Provider Address for University of Oklahoma PC 11 Computer
Next, standby counsel ask the Court to [o]rder the Government to (A) explain the reason for the discrepancy in IP addresses for the UO PC 11 computer, (B) confirm that the UO hard drive produced to the defense in discovery (129.15.110.31) comes from the computer used by Mr. Moussaoui at the University of Oklahoma, and (C) confirm that Mr. Moussaoui did not use any other UO computer. Reply at 11. Simply put, a typographical error exists in the Lawler Affidavit submitted by the Government. The correct internet provider address for University of Oklahoma PC 11 computer is 129.15.157.31. Sewell Affidavit at 18. As discussed in the first section of this pleading regarding authentication, a duplicate of the hard drive for PC 11 has been provided to the defense. As to whether Mr. Moussaoui used any other computer at the University of Oklahoma, only the defendant definitively knows the answer. The only evidence that the Government has regarding Mr. Moussaouis computer use at the University of Oklahoma involves PC 11 and PC 14, copies of which have been provided to the defense in discovery.
The Kinkos in Eagan, Minnesota
In their eighth request, standby counsel seek more information about the procedures used by Kinkos personnel and the steps they took to clean the Kinkos system and verify that no evidence of Mr. Moussaouis communications via Kinkos internet access still remains on the Kinkos system. Reply at 11. SSA Sewells affidavit describes in detail the procedures used by Kinkos to overwrite (clean) their systems. The affidavit reveals that during the month between the defendants use of the computers at Kinkos on August 12, 2001, and September 11, 2001, Kinkos cleaned their machines at least one time and perhaps many more, since their policy was to re-image (clean) the computers weekly. Sewell Affidavit at 12. Since September 11, 2001, the computers have been re-imaged several times and Kinkos personnel adamantly state that they are unable to recover any pre-existing data from a work station hard drive after the re-imaging process. Sewell Affidavit at 13. Further supporting the inability to locate references to xdesertman@hotmail.com is the fact that FBI CART examiners searched all data related to this e-mail account on both defendants and Mukkarum Alis laptops as well as the University of Oklahoma computers, none of which were ever cleansed or overwritten, and no data was found collaborating even the existence of any such account, or its use by the defendant. Sewell Affidavit at 15-17. Thus, there is no reason to believe that a search of the Kinkos computers in Eagan, Minnesota, would recover any relevant information about the defendants e-mail use on these computers. Sewell Affidavit at 17.7
____________________
7 Kinkos management states that they will no longer grant access to their computers without a search warrant. Sewell Affidavit at 12. Since the Government does not believe that any evidence would be recovered from these computers, it lacks any basis to seek a search warrant for the Kinkos computers.
Standby counsel next ask the Government to confirm that the file slack portions of Mukkarum Alis computer do not contain relevant information about Mr. Moussaouis use of the computer to send e-mails. Reply at 11. As previously stated in the first section of this pleading addressing authentication, the defense has an identical duplicate of what the Government has; therefore, they can search Mukkarum Alis computer as they wish. Moreover, FBI Cart Examiner Thomas Lawler thoroughly reviewed Mukkarum Alis computer, including the file slack portions, and found no relevant information. Sewell Affidavit at 15. Therefore, this request should be denied.
The Ghosting of the University of Oklahoma Computers
Standby counsel conclude their requests by asking the Government to identify the procedures employed by UO personnel to ghost the computer(s) allegedly used by Mr. Moussaoui and order the Government, despite the fact that it may be likely lost (see Lawler Affidavit at ¶ 28), to retrieve any forensic evidence showing use of those computers by Mr. Moussaoui and what he did while using those computers. Reply at 11. Calvin Weeks, the technical security officer for the University of Oklahoma, told the FBI that the University of Oklahoma used the commercial software Norton Ghost to restore a previously recorded hard drive image. Sewell Affidavit at 21. As to the second part of standby counsels request, the defense has in their possession a duplicate of University of Oklahoma PC 11 and PC 14; therefore, they can perform any investigation of these hard drives that the Government can. Therefore, this request should be denied.
Conclusion
The attached affidavit by SSA Sewell fully addresses the issues raised by standby counsel and demonstrates beyond question that the FBI properly and exhaustively examined all computer evidence in this case.
Respectfully Submitted,PAUL J. McNULTY
UNITED STATES ATTORNEYBy: /s/
Robert A. Spencer
Kenneth M. Karas
David J. Novak
Assistant United States Attorneys
CERTIFICATE OF SERVICE
I certify that on the 30th day of December, 2002, a copy of the foregoing Governments Response was provided to defendant Zacarias Moussaoui through the U.S. Marshals Service and faxed and mailed to the following::
Edward B. MacMahon, Jr., Esquire
107 East Washington Street
P.O. Box 903
Middleburg, Virginia 20118
fax: (540) 687-6366Frank W. Dunham, Jr., Esquire
Judy Clarke, Esquire
Public Defenders Office
Eastern District of Virginia
1650 King Street
Alexandria, Virginia 22314
Fax: (703) 600-0880Gerald Zerkin, Esquire
Assistant Public Defender
One Capital Square
Eleventh Floor
830 East Main Street
Richmond, Virginia 23219
fax: (804) 648-5033Alan H. Yamamoto, Esquire
108 N. Alfred Street
Alexandria, Virginia 22314
(703) 684-4700
fax: (703) 684-9700/s/
David J. Novak
Assistant United States Attorney
|
FOR THE EASTERN DISTRICT OF VIRGINIA Alexandria Division |
||
UNITED STATES OF AMERICA
v.ZACARIAS MOUSSAOUI, Defendant |
)
) ) ) ) ) ) |
Criminal No. 01-455-A |
AFFIDAVIT OF DARA K. SEWELL
I, Dara K. Sewell, being duly sworn, depose and say:
1. I am a Supervisory Special Agent with the Federal Bureau of Investigation. I have been a Special Agent for the FBI since 1996 and currently serve as the Computer Analysis Response Team (CART) Field Operations & Quality Program Manager. CART conducts forensic examinations of computers and other digital media evidence for the FBI, both at FBI Headquarters (HQ) and in 56 field divisions. In my current position, I am responsible for supervising field operations for 35 divisions and the development of CART procedures and practices as they relate to the forensic examination of computer evidence. I am knowledgeable in Macintosh, IBM Compatible, and UNIX platforms. I have completed CART forensic examiner training. As a CART Forensic Examiner, I have performed more than fifty (50) computer forensic examinations and assisted or supervised numerous others.
2. Prior to my current assignment, from 1996 to 2000, I was assigned to the FBI Pittsburgh Division as a Special Agent on the Regional White Collar Crime Squad and the High Technology Crime Task Force as an investigator and a CART Forensics Examiner. In 1999, I worked one-year as a full-time resident affiliate with the technical staff of Carnegie Mellon University Software Engineering Institute internationally recognized Computer Emergency Response Team (CERT) Coordination Center as a visiting scientist. Prior to joining the FBI, I was employed as a Senior Electrical Design Engineer with the Westinghouse Defense Center (WDC) in Baltimore, Maryland. During my 17-year tenure at WDC, I participated in the design, manufacturing, testing and production of various radar systems and test equipment. I possess a Bachelor of Science Degree from the University of Maryland in Electrical and Mechanical Engineering.
3. I have reviewed the affidavit of Special Agent Bridget Lawler dated September 4, 2002, and the affidavit for the defense of Mr. Donald Eugene Allison dated September 20, 2002, as well as numerous reports and records relating to this investigation. The following addresses issues raised by Mr. Allison.
Imaging and Authentication of Computer Hard Drive or Data
4. Much of Mr. Allisons affidavit addresses authentication issues regarding the hard drives provided in discovery. Authentication in this context means the process of ensuring that the duplicate of the hard drive provided in discovery is an exact copy of that which the FBI originally acquired. The FBI uses three different methods to duplicate or image a hard drive:
(1) GNU/Linux routine dd command via Red Hat Linux 7.1 (hereafter Linux dd);Generally speaking, FBI HQ CART procedures require, whenever possible, the use of computer forensic software hardware or firmware (hardware with software-like operating instructions/protocols designed into the hardware) that have undergone validation testing by CART or a qualified third party recognized by CART. While Mr. Allison favors Linux dd, the FBI has completed a series of tests validating both SafeBack (as of July 2001) and Logicube (as of May 2001). SafeBack imaging software or the Linux dd command are typically used by CART examiners if they have unlimited access and control over an original subject computer hard drive. In circumstances where time, access or control are limited (as in instances where a computer hard drive may not be seized but must be examined on site), CART examiners will gravitate towards the use of the SFK-000A hand-held disk duplicator by Logicube due to its relative speed, ease of use, and portability.(2) SafeBack version 2.18 imaging software by New Technologies (hereafter SafeBack);
(3) Solitaire Forensics Kit, SFK-000A hand-held disk duplicator by Logicube, Inc. (hereafter Logicube).
5. As Mr. Allison states in his affidavit, [m]any methods are available to create an exact duplicate [of computer data]. Allison Declaration at 3. However, Mr. Allison incorrectly asserts that only one method - the GNU/Linux routine dd - has been approved by the National Institute of Standards and Technologies. Allison Declaration at 3 (emphasis added). The National Institute of Standards and Technology (NIST) does oversee the Computer Forensic Tool Testing Project (CFTT); however, contrary to Mr. Allisons assertions, NIST does not approve any computer forensic tools. Instead, it merely reports the results of its testing. Moreover, Mr. Allison wrongly identifies Linux dd as the only one method . . . approved by [NIST]. Allisons Declaration at 3. First, the NIST report contained some criticisms of the Linux dd, none which have any bearing on this case.1 Second, NIST also evaluated SafeBack and voted to release its test results on December 13, 2002.2 Like the NIST report regarding Linux dd, the NIST report for SafeBack contained some criticisms which also have no apparent impact on this case.
____________________
1 See Test Results for Disk Imaging Tools: dd GNU fileutils 4.0.36, Provided with Red Hat Linux 7.1" which can be downloaded at www.ncjrs.org/pdffiles1/nij/196352.pdf.6. SafeBack: The computer forensic examiner executes SafeBack from a piece of removable media causing SafeBack to generate an image of the source digital media (e.g., hard drive) which then is saved to a digital medium, frequently Magneto-optical disks or digital tape (DAT tapes). Once the image is generated, the image may be verified. The image may later be restored to the same or a similar piece of media as the original source media (e.g., another hard drive). The restored image is the duplicate of the source hard drives data -- an accurate reproduction of the original hard drives data.2 The NIST SafeBack test report should be available at www.ojp.usdoj.gov/nij/sciencetech/ecrime.htm.
7. SafeBack imaging software has been utilized by computer forensic examiners in law enforcement for many years and the FBI has utilized it to successfully and accurately image hundreds, if not thousands, of computer hard drives. Moreover, the SafeBack software has been successfully validated by the FBI. In addition to FBIs testing, SafeBacks original producer, Sydex, Inc., as well as its current manufacturer, NTI, have completed extensive testing of SafeBack, which has consistently proven to accurately reproduce source data. Furthermore, SafeBack contains a self-verification program within the tool consisting of two write-error checking functions, which utilize hashes known as a cyclical redundancy checksum (CRC), to ensure that the SafeBack software is accurately duplicating a source hard drive bit by bit.
8. Logicube: Unlike SafeBack, the Logicube disk duplicator, is not software-based, does not generate an image of a source data set (e.g., hard drive) and then require the restoration of the image to similar digital medium (e.g., another hard drive). Instead, the Logicube disk duplicator operates more like a high speed cassette duplicator, typically with the original source hard drive connected at one end of the hand-held Logicube device, and another destination hard drive connected at the other end of the device designated to receive the data of the source drive. But, not unlike SafeBack, the Logicube hand-held disk duplicator uses CRC verification techniques to ensure that the duplicate data set generated accurately reflects the source data set (the original source hard drive). Although Logicube has not been submitted to NIST for evaluation as of this writing, hand-held disk-duplicators such as Logicube are widely accepted in the information and forensic communities. Moreover, like SafeBack, the FBI has utilized Logicube to successfully and accurately image hundreds of computer hard drives for almost two years and has subjected Logicube to the FBIs own validation. Finally, the manufacturer of Logicube completed extensive testing of its product prior to marketing it to ensure that the tool accurately reproduces source data.
Hash Values and Their Use to Authenticate Hard Drive Duplicates
9. In his affidavit, Mr. Allison writes: Further, once the duplicate has been created, a product such as the Message Digest version 5 (MD5) or the Secure Hash Algorithm version 1 (SHA-1) should be used to confirm that the duplication process has been done properly. Allison Affidavit at 3. Mr. Allison refers to programs that generate a unique value for both the data on the original hard drive and the data on a purported duplicate of that hard drive in order to further verify the results of the duplication process. These programs rely upon hashes to confirm that the duplication process has been done properly.
10. A hash is a colloquial reference to the number or value generated by the application of a mathematical formula to a specific data set (such as data in a computer file) in such a way so that it is extremely unlikely that the hash value represents any other data. In computer forensics, hashes may have many uses. A hash may be generated for a computer file prior to its duplication. After duplication, a hash may be generated on the duplicate. If the hash value of the original prior to duplication matches identically the hash value after the duplication, one may conclude that the duplicate file accurately reflects the data on the original file. The fact that the hash values match is typically more important than the hash values themselves.
11. There are a number of commonly accepted hash formulae and methods of running hashes in the computer forensic community, including the following: the Cyclical Redundancy Checksum (CRC), the Secure Hash Algorithm Version 1 (SHA-1), and the Message Digest Sum, Version 5 (MD5). Currently, CART techniques incorporate CRC and md5sum hashing methods.
12. Because SafeBack and the Logicube SFK-000A hand-held disk duplicator have been validated by CART as computer forensic imaging tools reliably capable of producing verifiable results, and because SafeBack and the Logicube SFK-000A incorporate reliable internal CRC verification techniques, CART procedures do not require examiners to generate separate MD5 or SH-1 hashes for computers imaged using SafeBack or Logicube SFK-000A disk duplicator. As such, absent a computer forensic examiner electing to generate such a hash on her own, there would not ordinarily be any MD5 or SH-1 hash values to disclose to the defense for any computer drives imaged with SafeBack or a Logicube disk duplicator.
CART Imaging Methods Used on Certain Computers of Interest
13. In the instant case, FBI reports indicate that the following computer hard drives were duplicated using the following approved methods:
(A) Zacarias Moussaouis Toshiba Laptop, serial number 11552157G, was duplicated/imaged using SafeBack on September 11, 2001, by Minneapolis FBI CART Field Examiner Jerry Dewees with a CRC32 value of 63b56fef.14. md5sum Hash Examination on Moussaouis Laptop: Notwithstanding CARTs belief that its reliance upon SafeBacks CRC verification functions is reasonable, in order to demonstrate the point, on October 15, 2002, I requested that the FBI CART Lab at FBI Headquarters do the following:(B) Mukkarum Alis Laptop, serial number 88914368A-1, was duplicated/imaged using SafeBack on September 16, 2001, by Oklahoma City FBI CART Field Examiner Timothy Ogiela with a CRC32 value of d7dcad55.
(C) University of Oklahoma PC 11 was duplicated/imaged using Logicubes disk duplicator on October 26, 2001, by Oklahoma City FBI CART Field Examiner Jeffrey Blasnitz with a CRC32 value of BABABD0A. Thereafter, the Logicube duplicate of PC 11 was imaged using SafeBack with a CRC value for the entire image of 7d235f08.
(D) University of Oklahoma PC 14, CPU serial number F6DM00B, was duplicated/imaged using Logicubes disk duplicator on October 26, 2001, by Oklahoma City FBI CART Field Examiner Timothy Ogiela with a CRC32 value of D4E0014D. Thereafter, the Logicube duplicate of PC 14 was imaged using SafeBack with a CRC value for the entire image of "6e1f373."
(A) Generate an md5sum hash on any partitions of the hard drive on Moussaouis original laptop computer, serial number 11552157G;15. On October 18, 2002, I was informed, in substance, by FBI HQ CART Examiner Lee Shepps of the following:(B) Restore the SafeBack image of the Moussaoui laptop to another drive (a duplicate) using the SafeBack image created by Minneapolis, MN FBI CART Field Examiner Jerry Dewees on September 11, 2001; and,
(C) Generate an md5sum hash on the primary partition of a restored SafeBack image of that hard drive (the duplicate) using the image generated by SA/FE DeWees on or about September 11, 2001.
(A) On October 18, 2002, CART Examiner Shepps restored the SafeBack image made by SA/FE Jerry DeWees on September 11, 2001, of the hard drive of Mr. Moussaouis Toshiba laptop, serial number 11552157G, to a hard drive;Thus, even using the defenses preferred md5sum hashing standard, the hash values for the only FAT32 partition on the original Moussaoui Toshiba laptop hard drive and that of the corresponding partition from the SafeBack restored image of that Moussaoui Toshiba laptop hard drive were one in the same.(B) On October 18, 2002, CART Examiner Shepps examined the restored SafeBack image of the Moussaoui laptop using a Linux Boot CD and found it to have only one primary partition (one FAT 32 partition);
(C) On October 18, 2002, CART Examiner Shepps executed a md5sum command (-b /dev/hda1) to generate a value for the restored SafeBack image of the Moussaoui Toshiba laptop hard drive and noted the value to be de12b076f9d6cc168fe3344dc1e07c58;
(D) On October 18, 2002, CART Examiner Shepps examined the original hard drive of the Moussaoui Toshiba laptop, serial number 11552157G using a Linux Boot CD and found it contained only one FAT 32 partition; and,
(E) On October 18, 2002, CART Examiner Shepps executed a md5sum command (-b /dev/hda1) to generate a value for the hard drive of the Moussaoui Toshiba laptop, serial number 11552157G, and noted the value to be de12b076f9d6cc168fe3344dc1e07c58.
16. md5sum Hash Examination on Mukkarum Alis Laptop: Similarly, on October 15, 2002, I also requested that the FBI CART Lab at FBI Headquarters do the following:
(A) Generate a md5sum hash on any partitions of Mukkarum Alis original laptop computer, serial number 88914368A-1;17. On October 18, 2002, I was informed, in substance, by FBI HQ CART Examiner Lee Shepps of the following:(B) Restore the SafeBack image of the Mukkarum Ali laptop to another drive (a duplicate) using the SafeBack image created by Minneapolis, MN FBI CART Field Examiner Timothy Ogiela on September 16, 2001; and
(C) Generate a md5sum hash on the primary partition of a restored SafeBack image of that hard drive using the image generated by SA/FE Ogiela on September 16, 2001.
(A) On October 18, 2002, CART Examiner Shepps restored the SafeBack image made by SA/FE Timothy Ogiela on September 16, 2001, of the hard drive of Mr. Mukkarum Alis laptop, serial number 88914368A-1, to a hard drive;Thus, even using the defenses preferred md5sum hashing standard, the hash values for the only FAT32 partition on the original Mukkarum Ali Toshiba laptop hard drive and that of the corresponding partition from the SafeBack restored image of that laptop hard drive were one in the same.(B) On October 18, 2002, CART Examiner Shepps examined the restored SafeBack image of the Ali laptop using a Linux Boot CD and found it to have only one FAT 32 partition;
(C) On October 18, 2002, CART Examiner Shepps executed a md5sum command (-b /dev/hda1) to generate a value for the restored SafeBack image of the Ali laptop and noted the value to be a665ee60525f795bd99703cd0666937b;
(D) On October 24, 2002, CART Examiner Shepps examined the original hard drive of the Ali laptop, serial number 88914368A-1, using a Linux Boot CD and found it contained one FAT32 partition; and,
(E) On October 24, 2002, CART Examiner Shepps executed a md5sum command (-b/dev/hda1) to generate a value for the hard drive of the Ali laptop, serial number 88914368A-1, and noted the value to be a665ee60525f795bd99703cd0666937b.
Moussaoui Laptop BIOS Settings
18. Defense counsel seek the BIOS (Basic Input/Output System) settings for Mr. Moussaouis laptop because the laptop had lost all power by the time of the Governments CART examination on August 6, 2002. A review of FBI records demonstrates that the Moussaoui Toshiba laptop, serial number 11552157G, was imaged by CART Field Examiner SA Jerry DeWees on September 11, 2001. At the time of generating the image, the Moussaoui Toshiba laptop did have power and SA DeWees made a record of the BIOS settings for the laptop. The BIOS settings for the Moussaoui Toshiba laptop were as follows:
Date per system: 9/11/2001Actual date: 9/11/2001
Time per system: 5:17 p.m.
Actual time: 4:58 p.m. [local CT]
Boot CART Floppy (implying Boot sequence is to A).
19. The Initial September 2001 Inquiry at the Eagan, MN Kinkos: On October 17, 2002, I spoke with Minneapolis FBI Special Agent David Rapp. At that time, SA Rapp told me that, to the best of SA Rapps unrefreshed recollection, on or about September 19, 2001, SA Rapp went to the Kinkos store in Eagan, Minnesota, to inquire about a receipt found on the person of Zacarias Moussaoui at the time of his arrest. At that time, SA Rapp met with a person who represented himself as a Kinkos employee responsible for managing and maintaining customer computer workstations. At that time, the Kinkos employee informed SA Rapp, in substance, as follows:
(A) The Kinkos receipt did indicate that a computer workstation had been utilized;
(B) It could not be determined from the copy of the Moussaoui receipt alone which computer workstation was used;
(C) In response to SA Rapps inquiry about the possibility of acquiring any information from the computer workstations regarding the use of the computers by Moussaoui, the Kinkos employee stated that, since the date of the receipt, all computers had been wiped clean/formatted and started with a fresh install; and,
(D) The computer workstations were generally wiped weekly or bi-weekly approximately, even though Kinkos policy called for weekly wipings. At a minimum, the Eagan Kinkos store wiped the computers at least once per month.
20. Inquiries to Corporate Kinkos: On October 11, 2002, I spoke with Timothy Cole, the Director of Loss Prevention for the Kinkos Corporation. Upon my inquiry about the possibility of obtaining hard drives (or images thereof) from the customer computer workstations in the Eagan Kinkos, Mr. Cole stated that Kinkos would not voluntarily comply with the request without a search warrant.
21. Eagan Follow-up: On October 11, 2002, I requested that the Minneapolis FBI Field Office contact Kinkos personnel at the Eagan store and determine if, as alleged by the defense, the Kinkos computer could still maintain evidence of defendant Zacarias Moussaouis use from August 2001. On or about October 15, 2002, Special Agents Brendan Hansen and Christopher Lester visited the Eagan Kinkos and interviewed Brian Fay, who, as of August 11, 2001, was one of two Kinkos employees who knew how to restore an image onto the six computers with internet access designated for customer use. Mr. Fay stated that the six computers presently at the store are the same computers (with the same hard drives) that were present in August of
2001. These six computers are leased and scheduled to be replaced at the end of this year. The computers are maintained by formatting the computers hard drives and reloading an image using Norton Ghost whenever business is slow and time allows. There are no logs recording the dates or frequency of loading images on to the computers and Fay could not estimate how frequently they were imaged. Although Fay was not personally familiar with the exact details of the formatting and imaging process he administers to the computers, Fay had been advised by Kinkos that the formatting and restoration process destroyed all files associated with previous users.
22. Kinkos Corporate Knowledge of its Internet Computer Maintenance Procedures: On various dates in October, 2002, I communicated with various individuals who identified themselves as computer network and computer security personnel working for the nationwide corporate offices of Kinkos Copy Centers. Throughout all but the very last of these discussions (the last being with Michael Menard, which is discussed below), the reoccurring and unwavering assertion of Kinkos personnel was that data could not be recovered from Kinkos customer computer workstations after the Kinkos re-imaging process had been completed.
23. On October 18, 2002, I spoke with Michael Menard, Kinkos Security Network Engineer, Field Support Department, in Oxford, CA. At that time, Mr. Menard informed me that Kinkos has a nationwide policy to re-image customer workstations, which he believed to be in effect in August 2001. The Kinkos re-imaging process consists of reinstalling baseline software to each customer workstation in the local branches using non-commercial compact disk read only memory (CD-ROM) disk sets custom-built by Kinkos engineers. Menard was not personally familiar with the exact details of the CD-ROM operations, but offered to contact Kinkos engineers.
24. On October 24, 2002, I again spoke with Mr. Michael Menard. At that time, he told me that, in August of 2001, Kinkos used a re-imaging baseline CD-ROM set version 8.3 in Eagan to re-image customer workstations. In March of 2002, Kinkos began using a new version CD-ROM set with updated software known as the Customer File Management Tool. The Customer File Management Tool runs automatically every four hours to delete temporary and cache files stored as a result of using internet browsers. The CD-ROM version 8.3 for Windows 95 system uses Symantecs Norton Ghost version 6.0 to transfer an image onto the customer workstation computers hard drive. Menard spoke with the Kinkos engineer who devised the imaging process and he stated that there is no way to retrieve data from a drive after re-imaging by this process. Kinkos branch personnel are told during training that, after the Ghost process is completed, no data can be retrieved from the hard drives. Finally, in response to SSA Sewells inquiry regarding the size of the computer hard drive and the image used by Ghost to overwrite a customer workstation, Menard was unable to identify the size of the replacement image or hard drive, but, after conferring off-line with an engineer, reiterated that, as a result of the re-formatting of the computer workstations hard drives, and the resulting overwriting of the hard drives partition tables, one would be unable to recover any pre-existing data from a workstation hard drive after the re-imaging/reformatting process employed by Kinkos, except, perhaps, in a laboratory.
The Likelihood of Recovering xdesertman@hotmail.com References
25. Results of Recent Search Efforts: On October 20, 2002, I was informed by FBI CART Field Examiner Thomas Lawler that he conducted an examination of certain computer data to locate any reference to xdesertman@hotmail.com and other e-mail addresses allegedly used by Mr. Moussaoui. On October 15-18, 2002, SA Lawler restored images and/or duplicated copies of the following computer hard drives to individual hard drives:
(A) Zacarias Moussaouis Toshiba Laptop, serial number 11552157G;Using the computer forensic software tool I-Look, SA Lawler ran a keyword text search of the data from each hard drive (which includes all file and unallocated space ("drive slack")) for xdesertman and as well as at least 27 variations of this account and other e-mail accounts associated with the investigation of this case. Keyword searches for all computers were negative.(B) Mukkarum Alis Laptop, serial number 88914368A-1;
(C) University of Oklahoma PC 11; CPU serial number 27DM008; and,
(D) University of Oklahoma PC 14, CPU serial number F6DM00B.
26. Present Likelihood of Recovery from Eagan Kinkos Computers: Based upon my experience, education, training and study, in my opinion, the present likelihood of recovering data attributable to Mr. Moussaouis use of an Eagan Kinkos computer to allegedly view the xdesertman@hotmail.com e-mail account is extremely remote. I base this opinion, in significant part, upon the following factors:
(A) Regardless of whether the Kinkos imaging process wipes the customer computer workstation hard drives prior to overlaying a baseline image, the fact remains that the reformatting and re-imaging process does significantly reduce the chances of recovering internet browser cache or temporary files, not merely because their partition table is overwritten, but because subsequent users then refill those temporary files with the records of their own internet use. In the instant case, the evidence corroborates the fact that the Eagan Kinkos customer computer workstations had been reformatted and overwritten prior to the visit by FBI agents on September 19, 2001;(B) All available evidence demonstrates that, since August 2001, the staff at the Eagan Kinkos Copy Center has reformatted and overwritten all customer computer workstations (which are the same which existed in August 2001) no less than once per month (an additional 13-14 times) with intervening use by customers during those periods, and potentially as often as once every week (potentially an additional 60 times). Moreover, since March of 2002, Kinkos began running software which is automatically scheduled every four (4) hours to delete all temporary and cache files generated by customer use;
(C) CART Forensic Examiner SA Thomas Lawler examined restored images of the Moussaoui laptop, the Mukkarum Ali laptop, and both University of Oklahoma computers using keywords likely to recover any references to the e-mail addresses allegedly used by Mr. Moussaoui, including the xdesertman@hotmail.com address, and found no such references;
(D) In comparison, the Mukkarum Ali laptop computer, which was not, to the best of the FBIs knowledge, reformatted or overwritten and which was alleged by the defense to have been used by Mr. Moussaoui to also view the xdessertman@hotmail.com account, were, by Mr. Allisons own admission, not found to contain any reference to that use. See Allison Declaration at 6;
(E) Even, in the event that a random remnant reference to xdesertman@hotmail.com could be found, it would be unlikely that such a reference could be excluded as not having come from intervening news reports (including the web broadcast of official court records of this court at http://notablecases.vaed.uscourts.gov/ ) relating to Mr. Moussaoui and xdesertman@hotmail.com. Indeed, in a recent search of the internet search engine at http://www.google.com/, at least 212 internet links were found to reference xdesertman including commercial news web links;
(F) As alluded to by SA Bridget Lawler, in the context of examining a computer hard drive which had been reformatted and overwritten numerous times, and re-used potentially by countless individuals, the ability to recover a random remnant of memory (a reference not to saved cache files, but to file slack) attributable to Mr. Moussaouis alleged use to view the xdesertman@hotmail.com account well over a year ago would, indeed, be a very rare find.
27. On October 9, 2002, I spoke with FBI SA Bridget Lawler, who told me that the discrepancy identified by Mr. Allison in his affidavit on page 7, paragraph 10(C), regarding the IP address assigned to PC 11 from the University of Oklahoma, was an error and should have read IP address 129.15.157.31. To the best of SA Lawlers knowledge, the duplicate computer drive provided to the defense in discovery for PC 11 was a duplicate of the correct computer hard drive corresponding to IP address 129.15.157.31 from the University of Oklahoma.
The Existence of Data outside the 10GB Partition on PC 11 from the Univ. of Oklahoma
28. The defense has expressed concern regarding the unexplained origin of extraneous data outside of the primary partition of the hard drive provided to them in discovery and represented to be a duplicate of the data on PC 11 from the University of Oklahoma. See Allison Declaration at 4. In order to properly answer these concerns, the defense returned their discovery copy of PC 11 to the Government. Based upon reports and conversations with Oklahoma City CART Field Examiner SA Jeffrey Blasnitz, FBI Field Examiner Thomas Lawler learned that, on or about October 24, 2001, SA Blasnitz generated a duplicate of a hard drive of PC 11 at the University of Oklahoma using a Solitaire SFK-000A Logicube disk-duplicator, version 1.15b. The Logicube duplicate hard drive receiving the duplicated data was approximately a 40 gigabyte (GB) (actually a 38.2 GB) hard drive. The Logicube SFK-000A duplicated 19, 999, 728 sectors. In generating the duplicate, SA Blasnitz declined the Logicube option to write zeros to the remaining target/destination drive space. Thereafter, SA Blasnitz generated a SafeBack image of the 40 GB Logicube duplicate of PC 11. On November 6, 2002, SA Lawler acquired the SafeBack image of PC 11 generated by SA Blasnitz, and restored it to a new, previously unused 40 GB hard drive (herein referred to as the SafeBack Restored Image HD). Beginning on November 6, 2002, SA Lawler examined the contents of Moussaoui PC 11 Discovery hard drive in comparison to the restored SafeBack image of PC 11 and found the following:
(A) The first 9.529 GB (out of the total 80 GBs) of the Moussaoui PC 11 Discovery hard drive is partition 0;
(B) The first 9.529 GB of the Moussaoui PC 11 Discovery HD is an exact copy of the data contained on the first 9.529 GBs of the restored SafeBack image of PC 11 (also in partition 0);
(C) On both the Moussaoui PC 11 Discovery hard drive and the SafeBack Restored Image, there begins at sector 19, 784, 836 of the drives a repeating pattern of 512 bytes of random data. That repeating pattern extended beyond the 9.529 GB partition 0 of both drives and continues for approximately 7.26 MB to end at sector 19, 999,728. [The exact number of sectors reported to have been duplicated by the Logicube SFK-000A from PC 11 produced by SA Blasnitz];
(D) Thereafter, on both the Moussaoui PC 11 Discovery hard drive and the SafeBack Restored Image there exists approximately 9.54 GBs of zeros (0) to end at sector 40,021,632 [the approximate middle of the 40 GB SafeBack Restored Image];
(E) Thereafter, on both the Moussaoui PC 11 Discovery hard drive and the SafeBack Restored Image, there exists 4 MB of data which is an exact duplicate of the first 4 MBs of data existing at the start of the hard drives (sectors 1 through and including 8,192);3
(F) Thereafter, on both the Moussaoui PC 11 Discovery HD and the SafeBack Restored Image, there exists approximately 18.18 Gigabytes (GB) of zeros (0). [To the end of the 40 Gigabyte (GB) SafeBack Restored Image HD];
(G) Thereafter, on the 80 GB Moussaoui PC 11 Discovery hard drive (which was approximately twice the size of the 40 GB SafeBack Restored Image), there exists zeros to the end of the that 80 Gigabyte (GB) hard drive.
___________________
3 Logicube Integrity Checks. On or about November 22, 2002, I spoke with Dr. Gideon Guy, the Technical Director for Logicube, Inc., and learned, in substance, the following: A) Dr. Guy has a doctorate in electrical engineering and has been involved in the field of computer hard drive imaging for 6-7 years. Dr. Guy has been with Logicube since March 1999; B) Designed into Logicube software v.1.15b was a standard unit integrity check which forced the Solitaire to verify the ability of the target hard drive (the drive onto which the duplicated data is to be placed) to read and write data (and therefore store data). This function occurred prior to Solitaire commencing the duplication process. The purpose of this function is twofold: 1) to assure that all cables are intact, all data bits have toggled at least once, and both drive interfaces are in good working order, and, 2) to determine the optimal speed to use with the subsequent duplication. The Logicube Solitaire would read the first 8,192 sectors (4 Megabytes) of the source drive (the original drive being copied) and write (duplicate) those sectors to the approximate middle of the target drive, then confirm that those sectors were properly written. This test function sequence always uses data obtained from the source drive and does not generate its own data for the test; C) Ordinarily, the integrity test data written to the target drive is overwritten by the ensuing duplicate image, or is overwritten by zeros when the Solitaire operator selects the option to write zeros to the end of the drive; D) If a source drive is substantially smaller than a target drive, and if the solitaire operator does not select the option to write zeros to the end of the target drive, some or all of the integrity test data may be observed on the target drive outside the partition which represents the duplicated data of the source drive; E) The existence of the integrity test data outside the partition on the target drive which represents the duplicated data of the source drive in no way undermines the accuracy of the duplicate data within the partition, and; F) In Logicube software version 1.17b and versions thereafter, the writability test sequence was altered to write the integrity test data to the first one quarter (1/4) of the target drive.All of which demonstrates that the duplicate of PC 11 within the 80 gigabyte hard drive provided to the defense accurately contains all of the data that existed on PC 11 at the time of duplication and was not contaminated by any outside data.
University of Oklahoma Ghost Imaging of PC 11 and PC 14
29. On December 17, 2002, Calvin Weeks, the technical security officer for the University of Oklahoma, advised me, in substance, that, during August of 2001, the University of Oklahoma used the commercial software Norton Ghost to restore a previously recorded hard drive image to the hard drives of the computers located in the computer laboratory, including PC 11 and PC 14.
Microsoft Hotmail and its Affiliates
30. In paragraph 10(B) on page 6 of his affidavit, Mr. Allison suggests that negative responses from hotmail regarding the existence of an xdesertman@hotmail.com e-mail account may not preclude the existence of such information in the records of affiliates of Hotmail or Microsoft. On November 22, 2002, I spoke with Tracy Ingle, Group Manager for Policy Enforcement for MSN Hotmail. Ms. Ingle was told of the nature of Mr. Allisons suggestion. In response, Ms. Ingle informed me that, MSN Hotmail subscriber information is not shared with other entities or third parties except as follows:
(A) Non-personally identifiable information (e.g., demographics information such as age, city, state and postal code) is shared with the MSN Hotmail marketing department;Moreover, according to Ms. Ingle, the search tools used by MSN Hotmail do not search such databases. A search for such information would require some degree of detailed information from the account holder to know what Microsoft services were actually used and when they were used in order to know where additional inquires could be made to possibly recover remnant references.(B) In 2001, account name, city, state and postal code were shared with INFOSPACE, a web-based publisher of an e-mail address directory, if, at the time of registering the account, the account subscriber did not elect to prohibit the sharing of this information;
(C) MSN Hotmail account e-mail is automatically deleted whenever the account subscriber fails to access the account for a period of thirty (30) days;
(D) A MSN Hotmail account is automatically deleted, and no record of it is thereafter maintained by MSN Hotmail, whenever the account subscriber fails to access the account for a period of 90 days;
(E) While, in theory, there could be references to a subsequently deleted hotmail e-mail account stored in data of other Microsoft services (e.g., a message posted to a MSN Group), such references would not be traceable to the registration information of that account holder as it would already have been deleted.
/s/Sworn to and subscribedDara K. Sewell
Supervisory Special Agent
Computer Analysis Response Team
Federal Bureau of Investigation
/s/
Sharon Dibbley
Notary Public
Alexandria, Virginia
My Commission Expires: 10/31/03
In this image released by the U.S. District Court, a government exhibit shows the INS arrest photo of Zacarias Moussaoui, that was introduced at the sentencing trial of admitted terrorist conspirator Zacarias Moussaoui. (U.S. District Court - Moussaoui trial exhibits and documents )